Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right product.
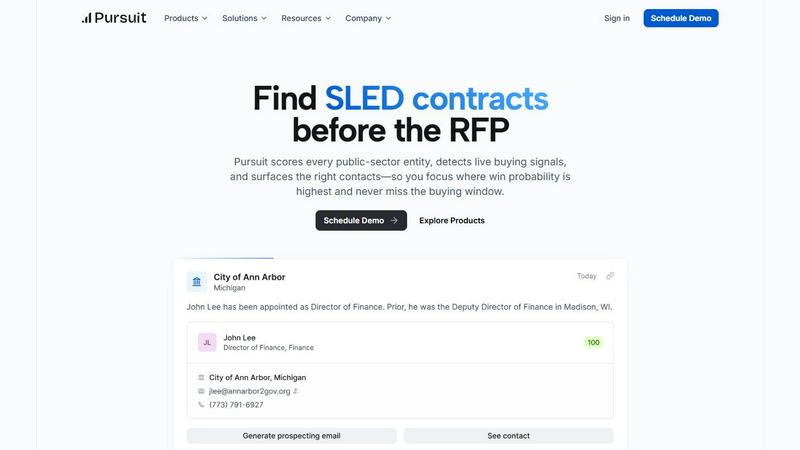
Pursuit
Pursuit helps you win government contracts by finding opportunities before they are officially announced.
Last updated: February 28, 2026
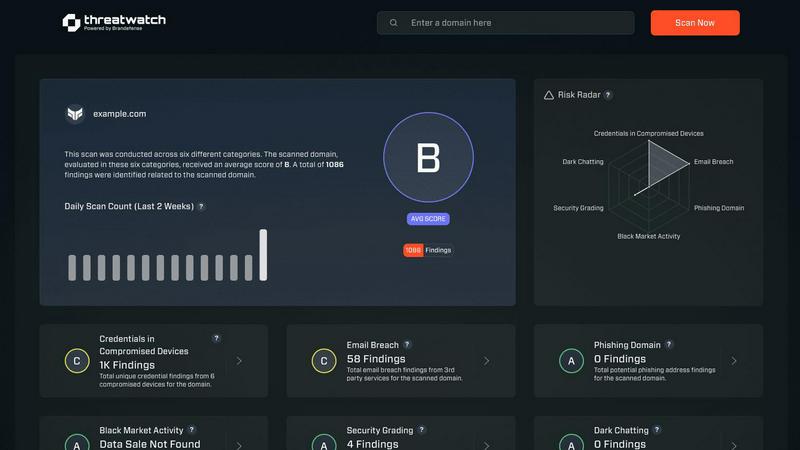
Threat Watch
Threat Watch quickly evaluates your cybersecurity health by identifying compromised accounts, devices, and dark web.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Signal Detection
Pursuit's core feature is its ability to uncover early-stage buying intentions long before a competitive bid is announced. The platform continuously monitors a vast array of public sector sources, including budget approvals, strategic plan mentions, and contract expiration notices. By analyzing this data, it surfaces specific signals that indicate an entity is preparing to procure a solution, allowing your team to engage during the planning phase and establish themselves as a knowledgeable partner rather than a late-stage bidder.
Entity Scoring & Prioritization
With over 110,000 SLED entities, knowing where to focus is critical. Pursuit scores and ranks every public sector organization based on live buying signals, budget alignment, and other key indicators. This scoring system automatically prioritizes accounts that are most likely to enter a buying cycle, enabling sales and marketing teams to allocate their time and resources efficiently towards the highest-probability opportunities, ensuring no critical budget window is missed.
Integrated Contact & Org Intelligence
Success requires reaching the right person. Pursuit provides essential contact information and dynamic org charts for each entity, which are continuously auto-enriched to maintain high accuracy. This includes identifying key decision-makers, understanding reporting structures, and tracking role changes. This foundational data ensures outreach is directed to relevant stakeholders and that relationship knowledge is preserved even when contacts move agencies or retire.
Native CRM & Workflow Integrations
To create a seamless workflow, Pursuit integrates directly with essential business tools like Salesforce and HubSpot. This bi-directional sync ensures that account scores, buying signals, and enriched contact data flow automatically into your existing CRM. This eliminates manual data entry, reduces enrichment time by over two-thirds, and ensures every team member—from marketing to customer success—operates from the same, up-to-date intelligence.
Threat Watch
Compromised Credentials Assessment
This feature allows organizations to automatically check for compromised credentials across various platforms. By monitoring leaked passwords and associated accounts, Threat Watch helps businesses identify accounts at risk, enabling them to take immediate action to secure their systems.
Vulnerable Device Identification
Threat Watch scans an organization's infrastructure to identify devices that are vulnerable to attacks. This includes evaluating the security status of all connected devices, ensuring that any potential weak points are addressed before they can be exploited by malicious actors.
Breached Account Monitoring
This feature continuously monitors known data breaches for any accounts associated with an organization. By providing alerts on compromised accounts, Threat Watch enables businesses to act swiftly to reset passwords and secure their digital assets, reducing the risk of unauthorized access.
Phishing Address Detection
Threat Watch actively identifies and flags known phishing addresses that may target the organization. By providing insights into potential phishing threats, businesses can educate their employees on recognizing these attempts, thus enhancing overall cybersecurity awareness.
Use Cases
Pursuit
For Sales Development Representatives (SDRs/BDRs)
SDRs stop guessing who to call. Pursuit provides daily, prioritized lists of accounts exhibiting live buying signals specific to their territory, such as recent budget approvals or contract expirations. This enables highly targeted, relevant outreach that resonates with the prospect's immediate needs, dramatically increasing cold call conversion rates and building a more qualified sales pipeline.
For Account Executives
Account Executives can walk into every meeting fully prepared. Using the Pursuit Chrome extension, they gain instant access to a comprehensive account dossier before a call. This includes known incumbents, historical contract values, the procurement vehicle, and a timeline of recent buying signals. This intelligence allows AEs to tailor their conversation, demonstrate deep understanding, and significantly improve their competitive win rates.
For Marketing Operations
Marketing teams can execute true account-based marketing (ABM) campaigns based on real-world intent. Pursuit allows them to build targeted audiences around accounts with verified budget allocations or new initiatives. These audiences can be synced directly to platforms like LinkedIn Ads, Marketo, or HubSpot, ensuring marketing efforts are precisely aligned with sales priorities and the public sector's budget cycles, leading to higher campaign conversion rates.
For Customer Success & Renewal Management
Customer Success teams gain proactive visibility into renewal and churn risks. Pursuit can be configured to send alerts 90-180 days before a customer's contract is set to expire. It also monitors for churn signals like budget cuts or competitor engagement at the account. This early warning system allows for timely renewal conversations and intervention, protecting revenue and strengthening client relationships.
Threat Watch
Small Business Cybersecurity
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides them with essential tools to monitor their cyber health, ensuring that they can identify vulnerabilities without overwhelming their limited resources.
Enterprise Risk Management
Large enterprises can utilize Threat Watch to maintain a comprehensive overview of their cybersecurity landscape. The tool’s real-time monitoring and assessment capabilities help in prioritizing risks across multiple departments and locations.
Incident Response Planning
Organizations can leverage Threat Watch to improve their incident response strategies. By understanding the vulnerabilities within their systems, businesses can develop tailored response plans, ensuring they are prepared to address potential cyber incidents effectively.
Cybersecurity Training and Awareness
Threat Watch helps organizations enhance employee awareness of cybersecurity threats. By identifying phishing addresses and compromised credentials, businesses can create training sessions that educate staff on recognizing and reporting potential threats.
Overview
About Pursuit
Pursuit is a pre-RFP intelligence platform designed to help businesses win contracts with state, local, and education (SLED) government entities. The fundamental challenge of selling to the public sector is its scale and complexity, with over 110,000 unique entities, each operating on its own budget cycles and procurement rules. Traditional sales methods, which often rely on personal relationships and reactive bidding, are insufficient in this environment. Pursuit addresses this by shifting the focus from who you know to what you know and when you know it. The platform systematically scans and analyzes public data—such as budget documents, council meeting minutes, and contract postings—to detect genuine buying signals 6 to 18 months before a formal Request for Proposal (RFP) is issued. This allows companies to identify opportunities early, understand the specific needs and procurement pathways, and engage with the right contacts at the optimal time. By providing this foundational intelligence, Pursuit enables government contractors, sales teams, and marketing operations to build a proactive, data-driven sales motion, significantly increasing pipeline growth, win rates, and operational efficiency while reducing research time and missed opportunities.
About Threat Watch
Threat Watch is a comprehensive cybersecurity intelligence solution aimed at empowering organizations to actively monitor and enhance their cyber health. By evaluating critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, Threat Watch provides users with a holistic view of their cybersecurity landscape. This tool is designed for businesses of all sizes, from small startups to large enterprises, helping them identify and prioritize potential risks effectively. The main value proposition of Threat Watch lies in its ability to deliver real-time insights and automated assessments, enabling organizations to quickly uncover vulnerabilities and exposures. By doing so, businesses can take proactive measures to mitigate risks and safeguard sensitive information, ensuring that they remain resilient against cyber threats. With Threat Watch, users gain clarity in their cybersecurity posture, allowing for swifter and more efficient responses to emerging threats.
Frequently Asked Questions
Pursuit FAQ
What types of buying signals does Pursuit detect?
Pursuit detects a wide range of early and concrete buying signals from the public sector. This includes mentions in approved budgets or capital improvement plans, discussions in city council or school board meeting minutes, the expiration dates of existing contracts, the posting of RFIs (Requests for Information), and leadership changes in relevant departments. These signals indicate an entity is actively researching or planning for a purchase.
How does Pursuit ensure data accuracy and relevance?
Pursuit maintains high data accuracy through a combination of automated monitoring of primary sources (official government websites and documents) and continuous data enrichment. The platform's systems regularly verify and update contact details, org charts, and contract information. This process ensures that the intelligence provided is current and reliable, with a reported 94% data accuracy rate for operational use.
Can Pursuit integrate with our existing tech stack (CRM, marketing automation)?
Yes, Pursuit is built for integration. It offers native, bi-directional integrations with major CRM platforms like Salesforce and HubSpot. This means account scores, contact details, and buying signals discovered in Pursuit can automatically sync to records in your CRM, and vice-versa. It also supports audience sync with marketing platforms such as Marketo and LinkedIn Campaign Manager.
Who within an organization is Pursuit designed for?
Pursuit is designed as a unified platform for the entire go-to-market team. It provides specific value for Sales Leaders in forecasting and coverage analysis, Revenue Operations in data management, Marketing in ABM campaign creation, Account Executives in deal strategy, Sales Development Representatives in outreach prioritization, and Customer Success Managers in renewal and retention planning.
Threat Watch FAQ
How does Threat Watch evaluate cyber health?
Threat Watch evaluates cyber health by analyzing critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, providing a comprehensive assessment of an organization's cybersecurity posture.
Is Threat Watch suitable for all business sizes?
Yes, Threat Watch is designed to be beneficial for organizations of all sizes, from small businesses to large enterprises. Its scalable features allow it to adapt to various cybersecurity needs.
How often does Threat Watch update its assessments?
Threat Watch provides real-time insights and assessments, ensuring that organizations receive the most current information about their cybersecurity status and any emerging threats.
Can Threat Watch integrate with other cybersecurity tools?
Yes, Threat Watch is designed to integrate seamlessly with other cybersecurity tools and platforms, allowing organizations to create a cohesive cybersecurity strategy that enhances their overall protection.
Alternatives
Pursuit Alternatives
Pursuit is a business intelligence platform designed to help companies win public sector contracts. It operates in the category of government sales intelligence, focusing on identifying opportunities, analyzing buyer propensity, and providing key contact information. This specialized focus makes it a powerful tool for businesses targeting the government market. Users often explore alternatives for several practical reasons. These can include budget constraints, the need for a different feature set, or a requirement for a platform that integrates with their specific technology stack. Some may seek a tool with a broader or narrower market focus than public sector contracts alone. When evaluating an alternative, it's crucial to assess a few core areas. First, ensure the platform's data source is reliable and covers the specific public sector entities you target. Second, confirm it provides actionable intelligence, like buying signals and contact details, not just raw data. Finally, consider how well it will integrate into your existing sales workflow and CRM to avoid creating extra work for your team.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence solution designed to provide organizations with insights into their cyber health. It falls under the category of business intelligence, focusing specifically on enhancing cybersecurity through real-time assessments and comprehensive vulnerability scanning. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms and systems. When looking for an alternative, it is essential to consider factors such as the comprehensiveness of the security assessments, the capability for real-time monitoring, and the overall usability of the platform. Prioritizing features that align with your organization’s unique security needs can help ensure that the alternative chosen effectively safeguards sensitive information and mitigates potential risks.
