Threat Watch
Threat Watch quickly evaluates your cybersecurity health by identifying compromised accounts, devices, and dark web.
Visit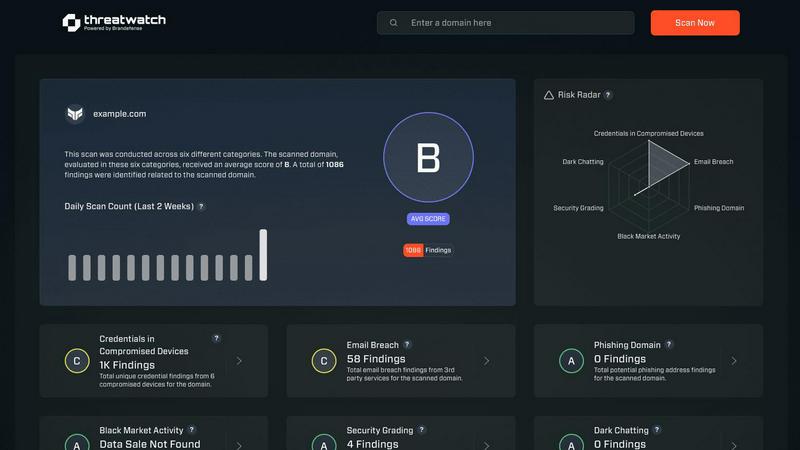
About Threat Watch
Threat Watch is a comprehensive cybersecurity intelligence solution aimed at empowering organizations to actively monitor and enhance their cyber health. By evaluating critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, Threat Watch provides users with a holistic view of their cybersecurity landscape. This tool is designed for businesses of all sizes, from small startups to large enterprises, helping them identify and prioritize potential risks effectively. The main value proposition of Threat Watch lies in its ability to deliver real-time insights and automated assessments, enabling organizations to quickly uncover vulnerabilities and exposures. By doing so, businesses can take proactive measures to mitigate risks and safeguard sensitive information, ensuring that they remain resilient against cyber threats. With Threat Watch, users gain clarity in their cybersecurity posture, allowing for swifter and more efficient responses to emerging threats.
Features of Threat Watch
Compromised Credentials Assessment
This feature allows organizations to automatically check for compromised credentials across various platforms. By monitoring leaked passwords and associated accounts, Threat Watch helps businesses identify accounts at risk, enabling them to take immediate action to secure their systems.
Vulnerable Device Identification
Threat Watch scans an organization's infrastructure to identify devices that are vulnerable to attacks. This includes evaluating the security status of all connected devices, ensuring that any potential weak points are addressed before they can be exploited by malicious actors.
Breached Account Monitoring
This feature continuously monitors known data breaches for any accounts associated with an organization. By providing alerts on compromised accounts, Threat Watch enables businesses to act swiftly to reset passwords and secure their digital assets, reducing the risk of unauthorized access.
Phishing Address Detection
Threat Watch actively identifies and flags known phishing addresses that may target the organization. By providing insights into potential phishing threats, businesses can educate their employees on recognizing these attempts, thus enhancing overall cybersecurity awareness.
Use Cases of Threat Watch
Small Business Cybersecurity
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides them with essential tools to monitor their cyber health, ensuring that they can identify vulnerabilities without overwhelming their limited resources.
Enterprise Risk Management
Large enterprises can utilize Threat Watch to maintain a comprehensive overview of their cybersecurity landscape. The tool’s real-time monitoring and assessment capabilities help in prioritizing risks across multiple departments and locations.
Incident Response Planning
Organizations can leverage Threat Watch to improve their incident response strategies. By understanding the vulnerabilities within their systems, businesses can develop tailored response plans, ensuring they are prepared to address potential cyber incidents effectively.
Cybersecurity Training and Awareness
Threat Watch helps organizations enhance employee awareness of cybersecurity threats. By identifying phishing addresses and compromised credentials, businesses can create training sessions that educate staff on recognizing and reporting potential threats.
Frequently Asked Questions
How does Threat Watch evaluate cyber health?
Threat Watch evaluates cyber health by analyzing critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, providing a comprehensive assessment of an organization's cybersecurity posture.
Is Threat Watch suitable for all business sizes?
Yes, Threat Watch is designed to be beneficial for organizations of all sizes, from small businesses to large enterprises. Its scalable features allow it to adapt to various cybersecurity needs.
How often does Threat Watch update its assessments?
Threat Watch provides real-time insights and assessments, ensuring that organizations receive the most current information about their cybersecurity status and any emerging threats.
Can Threat Watch integrate with other cybersecurity tools?
Yes, Threat Watch is designed to integrate seamlessly with other cybersecurity tools and platforms, allowing organizations to create a cohesive cybersecurity strategy that enhances their overall protection.
Explore more in this category:
Similar to Threat Watch
Generate unique and memorable business names effortlessly with our free AI Business Name Generator, perfect for startups and brands.
Run Smarter Surveys and Turn Feedback Into Actionable Insights
MarketWrk automates CPG pricing, MAP monitoring, and review tracking, empowering teams with instant insights to optimize sales and protect margins.
Opal44 transforms your website traffic data into clear, actionable insights without the jargon, making analytics easy.
Fusedash transforms raw data into intuitive dashboards and charts, enabling your team to act on insights swiftly.
finban simplifies liquidity planning, empowering confident decisions on hiring, taxes, and investments without Excel.
Zignt is a contract management tool that helps teams create, send, and sign legally binding agreements quickly.
aVenture is an AI platform that delivers comprehensive insights on private companies, investors, and venture capital.
