iGPT vs Threat Watch
Side-by-side comparison to help you choose the right product.
iGPT delivers secure, context-aware answers from email data, streamlining enterprise workflows with immediate.
Last updated: February 28, 2026
Threat Watch
Threat Watch quickly evaluates your cybersecurity health by identifying compromised accounts, devices, and dark web.
Last updated: March 1, 2026
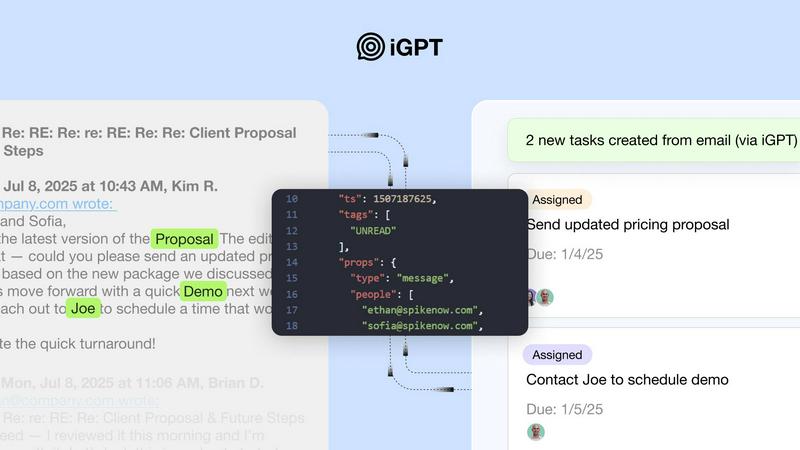
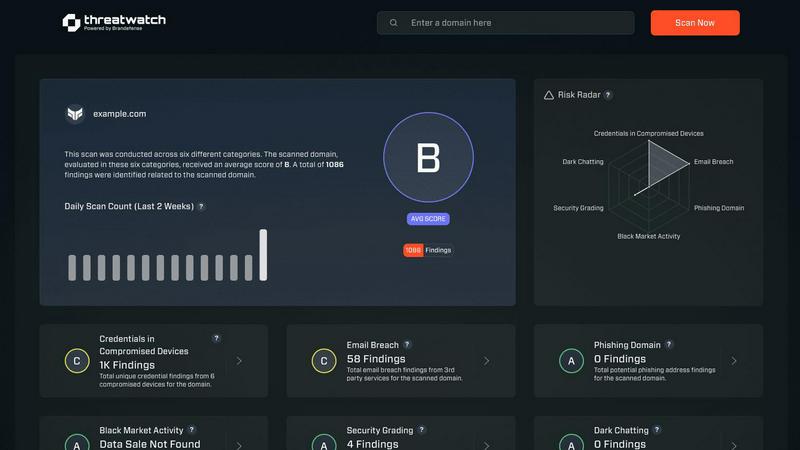
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Immediate Integration
iGPT offers an easy integration experience with its SDK and live playground, allowing developers to test requests and responses quickly. This feature ensures that teams can get up and running with minimal hassle, enabling rapid deployment of AI solutions.
Contextual Responses
iGPT provides contextual responses that are ready for reasoning and automation. Each response includes citations to the source data, allowing users to trace back the information to its origin. This feature ensures that all insights are reliable and verifiable.
Hybrid Retrieval
The API employs a hybrid retrieval system that combines semantic, keyword, and filter-based searches. This approach allows for comprehensive data extraction and ensures that users receive the most relevant information in a single API call, enhancing efficiency and accuracy.
Continuous Data Indexing
iGPT continuously indexes new messages and attachments in real time. This feature ensures that the data and answers are always up-to-date, allowing users to rely on the most current information when making business decisions.
Threat Watch
Compromised Credentials Assessment
This feature allows organizations to automatically check for compromised credentials across various platforms. By monitoring leaked passwords and associated accounts, Threat Watch helps businesses identify accounts at risk, enabling them to take immediate action to secure their systems.
Vulnerable Device Identification
Threat Watch scans an organization's infrastructure to identify devices that are vulnerable to attacks. This includes evaluating the security status of all connected devices, ensuring that any potential weak points are addressed before they can be exploited by malicious actors.
Breached Account Monitoring
This feature continuously monitors known data breaches for any accounts associated with an organization. By providing alerts on compromised accounts, Threat Watch enables businesses to act swiftly to reset passwords and secure their digital assets, reducing the risk of unauthorized access.
Phishing Address Detection
Threat Watch actively identifies and flags known phishing addresses that may target the organization. By providing insights into potential phishing threats, businesses can educate their employees on recognizing these attempts, thus enhancing overall cybersecurity awareness.
Use Cases
iGPT
Email Assistants
iGPT enables the creation of intelligent email assistants that can draft, prioritize, and act on emails with full context. This use case enhances productivity by automating routine tasks and ensuring important actions are not overlooked.
Workflow Automation
With iGPT, organizations can transform email threads into actionable tasks, deadlines, and approval requests. This streamlines workflows and helps teams keep track of progress, making it easier to manage projects and ensure nothing gets stuck.
Customer Support Copilots
Customer support teams can utilize iGPT to reconstruct the full customer story across long email chains and attachments. This capability allows support agents to understand the history and tone of conversations, improving the quality of customer interactions.
Compliance and Audit Trails
iGPT aids in compliance by providing a clear audit trail of feedback, approvals, and rationale linked back to original conversations. This feature is crucial for organizations that require transparency and accountability in their communication processes.
Threat Watch
Small Business Cybersecurity
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides them with essential tools to monitor their cyber health, ensuring that they can identify vulnerabilities without overwhelming their limited resources.
Enterprise Risk Management
Large enterprises can utilize Threat Watch to maintain a comprehensive overview of their cybersecurity landscape. The tool’s real-time monitoring and assessment capabilities help in prioritizing risks across multiple departments and locations.
Incident Response Planning
Organizations can leverage Threat Watch to improve their incident response strategies. By understanding the vulnerabilities within their systems, businesses can develop tailored response plans, ensuring they are prepared to address potential cyber incidents effectively.
Cybersecurity Training and Awareness
Threat Watch helps organizations enhance employee awareness of cybersecurity threats. By identifying phishing addresses and compromised credentials, businesses can create training sessions that educate staff on recognizing and reporting potential threats.
Overview
About iGPT
iGPT is an enterprise-grade API designed to empower businesses by providing a foundational intelligence layer for AI agents and workflows. It addresses a critical challenge in the modern workplace: the vast amounts of unstructured data found in emails and communications. While these channels are where real business transactions occur, they often confound traditional AI systems due to their conversational nature and heavy use of attachments. By transforming complex email threads, documents, and spreadsheets into context-aware, actionable insights, iGPT enables developers and enterprises to create intelligent systems that enhance sales, customer success, and compliance solutions. Its primary value proposition lies in its simplicity and security, as it streamlines the complex processes of data parsing and context extraction into a single, unified API call. This ensures that teams can deliver intelligent features rapidly, all while maintaining stringent security protocols and comprehensive audit trails, ensuring that sensitive data remains under the company's control and is not used for model training.
About Threat Watch
Threat Watch is a comprehensive cybersecurity intelligence solution aimed at empowering organizations to actively monitor and enhance their cyber health. By evaluating critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, Threat Watch provides users with a holistic view of their cybersecurity landscape. This tool is designed for businesses of all sizes, from small startups to large enterprises, helping them identify and prioritize potential risks effectively. The main value proposition of Threat Watch lies in its ability to deliver real-time insights and automated assessments, enabling organizations to quickly uncover vulnerabilities and exposures. By doing so, businesses can take proactive measures to mitigate risks and safeguard sensitive information, ensuring that they remain resilient against cyber threats. With Threat Watch, users gain clarity in their cybersecurity posture, allowing for swifter and more efficient responses to emerging threats.
Frequently Asked Questions
iGPT FAQ
What types of data can iGPT process?
iGPT can process various forms of unstructured data, including emails, documents, PDFs, and spreadsheets, turning them into actionable insights.
How does iGPT ensure data security?
iGPT employs enterprise-grade security measures, including role-based access control and zero data retention policies, ensuring that sensitive data remains under the company's control and is not used for model training.
Can iGPT integrate with existing systems?
Yes, iGPT is designed for immediate integration, with SDKs and a live playground that allows developers to test and connect email sources quickly.
What is the response time for iGPT?
iGPT typically delivers responses with around 200 milliseconds for retrieval and approximately 3 seconds to generate the first token, even when dealing with large, complex email data.
Threat Watch FAQ
How does Threat Watch evaluate cyber health?
Threat Watch evaluates cyber health by analyzing critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, providing a comprehensive assessment of an organization's cybersecurity posture.
Is Threat Watch suitable for all business sizes?
Yes, Threat Watch is designed to be beneficial for organizations of all sizes, from small businesses to large enterprises. Its scalable features allow it to adapt to various cybersecurity needs.
How often does Threat Watch update its assessments?
Threat Watch provides real-time insights and assessments, ensuring that organizations receive the most current information about their cybersecurity status and any emerging threats.
Can Threat Watch integrate with other cybersecurity tools?
Yes, Threat Watch is designed to integrate seamlessly with other cybersecurity tools and platforms, allowing organizations to create a cohesive cybersecurity strategy that enhances their overall protection.
Alternatives
iGPT Alternatives
iGPT is an enterprise-grade API designed to enhance business intelligence by providing contextual answers directly from email data. It serves as a foundational intelligence layer for AI agents and workflows, addressing the challenges posed by the unstructured nature of emails and communication data. Users often seek alternatives to iGPT due to factors such as pricing, specific feature requirements, or compatibility with different platforms. When exploring alternatives, it is essential to consider the ease of integration, the level of security offered, and the ability to process complex data types effectively to ensure that the chosen solution meets your organization's unique needs.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence solution designed to provide organizations with insights into their cyber health. It falls under the category of business intelligence, focusing specifically on enhancing cybersecurity through real-time assessments and comprehensive vulnerability scanning. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms and systems. When looking for an alternative, it is essential to consider factors such as the comprehensiveness of the security assessments, the capability for real-time monitoring, and the overall usability of the platform. Prioritizing features that align with your organization’s unique security needs can help ensure that the alternative chosen effectively safeguards sensitive information and mitigates potential risks.