CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right product.
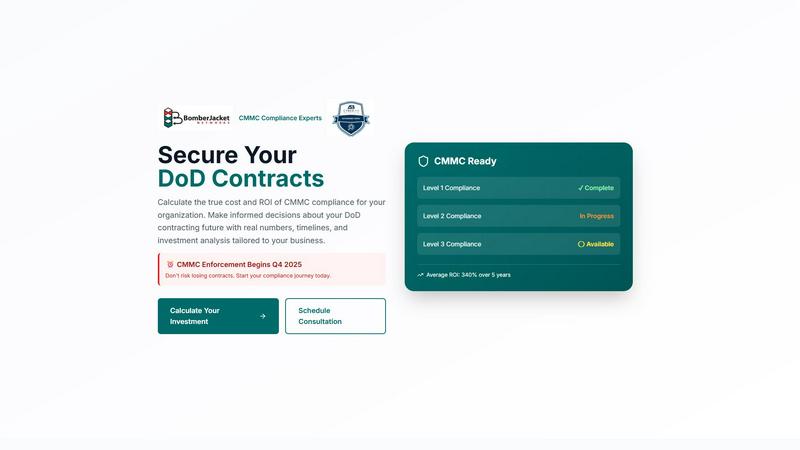
CMMC ROI
Calculate the ROI of CMMC compliance to secure DoD contracts and make informed investment decisions for your future.
Last updated: March 1, 2026
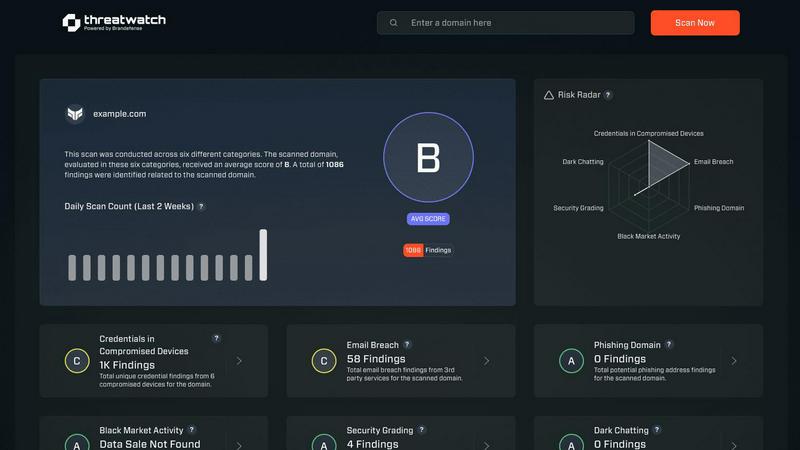
Threat Watch
Threat Watch quickly evaluates your cybersecurity health by identifying compromised accounts, devices, and dark web.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
ROI Calculations
CMMC ROI provides detailed ROI calculations that help organizations understand the financial implications of achieving CMMC certification. By analyzing the costs versus the potential revenue protection, contractors can make informed investment decisions.
Risk Assessments
The tool includes comprehensive risk assessments that identify vulnerabilities within an organization’s cybersecurity framework. This feature helps contractors understand their current risk levels and the importance of compliance in mitigating those risks.
Tailored Investment Analyses
CMMC ROI offers tailored investment analyses based on the specific size and revenue of the contractor's business. This personalization ensures that the calculations reflect realistic scenarios, helping organizations plan their financial commitments accurately.
Implementation Timeline
CMMC ROI lays out a clear 12-month implementation timeline for achieving CMMC Level 2 certification. This structured approach helps contractors manage their compliance journey effectively, ensuring that all necessary steps are completed in a timely manner.
Threat Watch
Compromised Credentials Assessment
This feature allows organizations to automatically check for compromised credentials across various platforms. By monitoring leaked passwords and associated accounts, Threat Watch helps businesses identify accounts at risk, enabling them to take immediate action to secure their systems.
Vulnerable Device Identification
Threat Watch scans an organization's infrastructure to identify devices that are vulnerable to attacks. This includes evaluating the security status of all connected devices, ensuring that any potential weak points are addressed before they can be exploited by malicious actors.
Breached Account Monitoring
This feature continuously monitors known data breaches for any accounts associated with an organization. By providing alerts on compromised accounts, Threat Watch enables businesses to act swiftly to reset passwords and secure their digital assets, reducing the risk of unauthorized access.
Phishing Address Detection
Threat Watch actively identifies and flags known phishing addresses that may target the organization. By providing insights into potential phishing threats, businesses can educate their employees on recognizing these attempts, thus enhancing overall cybersecurity awareness.
Use Cases
CMMC ROI
Small Contractor Compliance
A small contractor with 1-50 employees generating $2.5M in DoD contracts can use CMMC ROI to calculate a 5-year investment of $721K-$881K for Level 2 compliance. This helps them understand their financial commitment and the potential ROI.
Medium Contractor Planning
Medium-sized contractors with 51-250 employees and $10M in annual DoD revenue can utilize CMMC ROI to evaluate their investment of approximately $1.14M-$1.44M for CMMC Level 2 compliance. This allows them to assess the risk of losing contracts and how compliance can enhance their competitive advantage.
Large Contractor Strategy
A large contractor with over 250 employees and $50M in DoD contracts can leverage CMMC ROI to calculate their investment, which ranges from $1.78M-$2.23M for Level 2 compliance. This assists them in making strategic decisions regarding their cybersecurity investments.
Technology Firm Evaluation
Technology firms with $15M in DoD contracts can use CMMC ROI to analyze the costs involved in achieving CMMC compliance and to understand the investment's potential returns, ultimately aiding in securing contracts and maintaining market competitiveness.
Threat Watch
Small Business Cybersecurity
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides them with essential tools to monitor their cyber health, ensuring that they can identify vulnerabilities without overwhelming their limited resources.
Enterprise Risk Management
Large enterprises can utilize Threat Watch to maintain a comprehensive overview of their cybersecurity landscape. The tool’s real-time monitoring and assessment capabilities help in prioritizing risks across multiple departments and locations.
Incident Response Planning
Organizations can leverage Threat Watch to improve their incident response strategies. By understanding the vulnerabilities within their systems, businesses can develop tailored response plans, ensuring they are prepared to address potential cyber incidents effectively.
Cybersecurity Training and Awareness
Threat Watch helps organizations enhance employee awareness of cybersecurity threats. By identifying phishing addresses and compromised credentials, businesses can create training sessions that educate staff on recognizing and reporting potential threats.
Overview
About CMMC ROI
CMMC ROI is a comprehensive compliance solution developed specifically for contractors working with the Department of Defense (DoD) who need to navigate the intricate requirements of the Cybersecurity Maturity Model Certification (CMMC). Offered by BomberJacket Networks, a service-disabled veteran-owned business with over two decades of cybersecurity experience, CMMC ROI is designed to empower organizations to successfully manage their compliance journey. This tool provides detailed return on investment (ROI) calculations, risk assessments, and customized investment analyses, enabling contractors to understand both the costs and potential benefits associated with achieving CMMC certification. With a remarkable success rate of 99%, CMMC ROI not only facilitates securing DoD contracts but also enhances competitive positioning in anticipation of the enforcement deadline in Q4 2025. By leveraging CMMC ROI, contractors can make informed decisions about their compliance strategies, ensuring they remain competitive and protected in a rapidly evolving cyber landscape.
About Threat Watch
Threat Watch is a comprehensive cybersecurity intelligence solution aimed at empowering organizations to actively monitor and enhance their cyber health. By evaluating critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, Threat Watch provides users with a holistic view of their cybersecurity landscape. This tool is designed for businesses of all sizes, from small startups to large enterprises, helping them identify and prioritize potential risks effectively. The main value proposition of Threat Watch lies in its ability to deliver real-time insights and automated assessments, enabling organizations to quickly uncover vulnerabilities and exposures. By doing so, businesses can take proactive measures to mitigate risks and safeguard sensitive information, ensuring that they remain resilient against cyber threats. With Threat Watch, users gain clarity in their cybersecurity posture, allowing for swifter and more efficient responses to emerging threats.
Frequently Asked Questions
CMMC ROI FAQ
What is CMMC ROI?
CMMC ROI is a compliance solution designed to assist DoD contractors in navigating the CMMC requirements, providing them with ROI calculations, risk assessments, and investment analyses tailored to their specific needs.
How does CMMC ROI calculate ROI?
CMMC ROI calculates ROI by taking the protected value from 5-year DoD revenue and the estimated cost of breaches avoided, then comparing it against the total investment made for compliance, enabling contractors to see the financial benefits of achieving certification.
What is the implementation timeline for CMMC compliance?
The implementation timeline for CMMC compliance is structured over 12 months, covering essential phases such as gap assessment, remediation, documentation, assessment preparation, and final certification, ensuring a systematic approach to compliance.
Why is CMMC compliance important for contractors?
CMMC compliance is crucial for contractors as it secures their eligibility for DoD contracts. Without certification, contractors face a 100% risk of losing contracts, making compliance vital for business continuity and competitive advantage.
Threat Watch FAQ
How does Threat Watch evaluate cyber health?
Threat Watch evaluates cyber health by analyzing critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, providing a comprehensive assessment of an organization's cybersecurity posture.
Is Threat Watch suitable for all business sizes?
Yes, Threat Watch is designed to be beneficial for organizations of all sizes, from small businesses to large enterprises. Its scalable features allow it to adapt to various cybersecurity needs.
How often does Threat Watch update its assessments?
Threat Watch provides real-time insights and assessments, ensuring that organizations receive the most current information about their cybersecurity status and any emerging threats.
Can Threat Watch integrate with other cybersecurity tools?
Yes, Threat Watch is designed to integrate seamlessly with other cybersecurity tools and platforms, allowing organizations to create a cohesive cybersecurity strategy that enhances their overall protection.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a comprehensive compliance solution tailored for Department of Defense contractors. It falls under the category of business intelligence, designed to assist organizations in navigating the Cybersecurity Maturity Model Certification landscape. Users often seek alternatives to CMMC ROI due to factors such as pricing, specific feature sets, or compatibility with their existing platforms and workflows. When evaluating potential alternatives, it is essential to consider aspects like ease of use, the comprehensiveness of compliance support, and the ability to generate personalized ROI calculations that align with the unique needs of your business.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence solution designed to provide organizations with insights into their cyber health. It falls under the category of business intelligence, focusing specifically on enhancing cybersecurity through real-time assessments and comprehensive vulnerability scanning. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms and systems. When looking for an alternative, it is essential to consider factors such as the comprehensiveness of the security assessments, the capability for real-time monitoring, and the overall usability of the platform. Prioritizing features that align with your organization’s unique security needs can help ensure that the alternative chosen effectively safeguards sensitive information and mitigates potential risks.
