Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right product.

Deeploy
Deeploy provides essential governance to safely manage and scale your AI systems.
Last updated: March 1, 2026
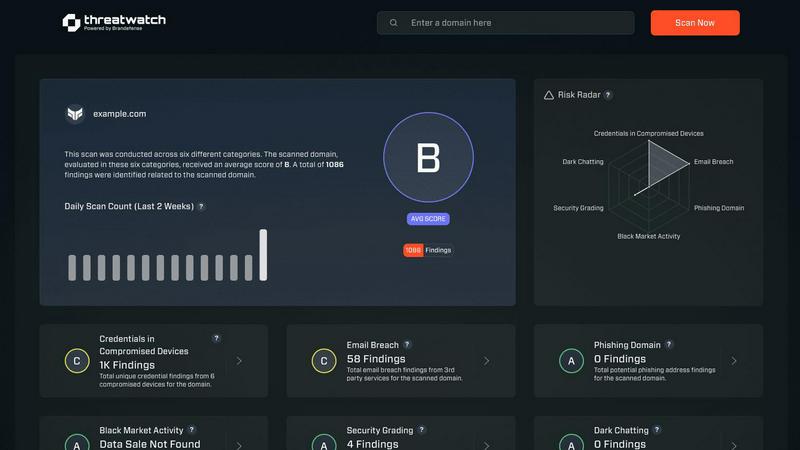
Threat Watch
Threat Watch quickly evaluates your cybersecurity health by identifying compromised accounts, devices, and dark web.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
This feature provides the essential first step of governance: complete visibility. It allows organizations to discover, onboard, and manage every AI system from a single interface. By connecting to existing MLOps or GenAI platforms, it eliminates blind spots without forcing painful migrations. This creates a centralized inventory and documentation hub, which is the foundational layer for all subsequent governance and control activities, ensuring no AI system operates in the shadows.
Control Frameworks
Deeploy simplifies regulatory compliance by providing structured, guided workflows. Organizations can choose from default frameworks based on major standards like ISO 42001 and the NIST AI RMF, or build custom ones tailored to their specific needs. This feature helps teams classify AI system risk levels in minutes and establishes clear accountability through defined approval processes. It turns complex regulatory requirements into a manageable, straightforward path to compliance.
Control Implementation
This feature translates governance policies into enforceable, practical actions for engineering teams. It gives developers clear and actionable requirements for each AI system, avoiding vague guidelines. Compliance is accelerated by up to 90% through the use of pre-built templates and the automatic collection of audit evidence. Furthermore, it employs AI-powered assessments to handle repetitive compliance checks, making governance a seamless part of the development workflow.
Real-Time Monitoring
Proactive risk prevention is achieved through continuous, real-time monitoring of AI performance in production. The system provides instant alerts for critical issues like model drift, performance degradation, or output anomalies, allowing teams to act before users are impacted. It also adds crucial tracing and guardrails to protect Large Language Model (LLM) outputs, ensuring AI systems behave as intended and remain compliant with safety standards over time.
Threat Watch
Compromised Credentials Assessment
This feature allows organizations to automatically check for compromised credentials across various platforms. By monitoring leaked passwords and associated accounts, Threat Watch helps businesses identify accounts at risk, enabling them to take immediate action to secure their systems.
Vulnerable Device Identification
Threat Watch scans an organization's infrastructure to identify devices that are vulnerable to attacks. This includes evaluating the security status of all connected devices, ensuring that any potential weak points are addressed before they can be exploited by malicious actors.
Breached Account Monitoring
This feature continuously monitors known data breaches for any accounts associated with an organization. By providing alerts on compromised accounts, Threat Watch enables businesses to act swiftly to reset passwords and secure their digital assets, reducing the risk of unauthorized access.
Phishing Address Detection
Threat Watch actively identifies and flags known phishing addresses that may target the organization. By providing insights into potential phishing threats, businesses can educate their employees on recognizing these attempts, thus enhancing overall cybersecurity awareness.
Use Cases
Deeploy
Centralized AI Registry for Large Enterprises
Large organizations with AI scattered across different departments and vendors use Deeploy to create a single source of truth. This central registry provides executives and compliance officers with immediate oversight of all AI initiatives, documenting each system's purpose, risk classification, and owner. This foundational inventory is critical for audit readiness and strategic management of AI investments at scale.
Streamlining EU AI Act Compliance
Companies operating in or selling to the European Union leverage Deeploy to navigate the stringent requirements of the EU AI Act. The platform's guided workflows help them correctly classify their AI systems by risk level, implement the necessary controls, and automatically generate the documentation and evidence required to demonstrate compliance, significantly reducing legal and reputational risk.
Enabling Safe AI in Regulated Healthcare
Healthcare providers and technology firms, like mental health platform NiceDay, use Deeploy to deploy AI responsibly. The platform's explainability features and expert feedback loops are crucial for clinical settings. It allows professionals to understand AI-driven recommendations and provide oversight, ensuring patient safety and building the trust necessary to integrate AI into sensitive care pathways.
Accelerating Model Deployment with Governance
Data science and AI teams use Deeploy to accelerate their MLOps lifecycle while embedding governance from the start. The platform reduces model deployment time from weeks to hours while automatically applying the right monitoring and documentation controls. This gives technical teams the speed they need and provides non-technical stakeholders, like customer service or compliance, with the transparency they require.
Threat Watch
Small Business Cybersecurity
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides them with essential tools to monitor their cyber health, ensuring that they can identify vulnerabilities without overwhelming their limited resources.
Enterprise Risk Management
Large enterprises can utilize Threat Watch to maintain a comprehensive overview of their cybersecurity landscape. The tool’s real-time monitoring and assessment capabilities help in prioritizing risks across multiple departments and locations.
Incident Response Planning
Organizations can leverage Threat Watch to improve their incident response strategies. By understanding the vulnerabilities within their systems, businesses can develop tailored response plans, ensuring they are prepared to address potential cyber incidents effectively.
Cybersecurity Training and Awareness
Threat Watch helps organizations enhance employee awareness of cybersecurity threats. By identifying phishing addresses and compromised credentials, businesses can create training sessions that educate staff on recognizing and reporting potential threats.
Overview
About Deeploy
Deeploy is a foundational AI governance platform designed to give organizations complete control over their artificial intelligence systems. At its core, the product addresses a fundamental business challenge: how to harness the power of AI for transformation while systematically managing its inherent risks. It provides the essential infrastructure that is often missing from modern AI stacks, moving companies from a state of fragmented, ungoverned AI deployment to one of centralized oversight and compliance. Deeploy is built for technology, healthcare, finance, and other sectors where AI is critical to operations and subject to strict regulations like the EU AI Act. Its primary value proposition is enabling businesses to scale their AI initiatives faster and with greater confidence by implementing clear governance, reducing operational risk, and building necessary trust through transparency and documentation.
About Threat Watch
Threat Watch is a comprehensive cybersecurity intelligence solution aimed at empowering organizations to actively monitor and enhance their cyber health. By evaluating critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, Threat Watch provides users with a holistic view of their cybersecurity landscape. This tool is designed for businesses of all sizes, from small startups to large enterprises, helping them identify and prioritize potential risks effectively. The main value proposition of Threat Watch lies in its ability to deliver real-time insights and automated assessments, enabling organizations to quickly uncover vulnerabilities and exposures. By doing so, businesses can take proactive measures to mitigate risks and safeguard sensitive information, ensuring that they remain resilient against cyber threats. With Threat Watch, users gain clarity in their cybersecurity posture, allowing for swifter and more efficient responses to emerging threats.
Frequently Asked Questions
Deeploy FAQ
What is AI governance and why is it important?
AI governance is the framework of policies, processes, and tools used to ensure AI systems are developed and used responsibly, ethically, and in compliance with regulations. It is important because as AI scales within an organization, the risks-scale too. Without governance, companies face potential legal penalties, reputational damage from AI failures, and operational inefficiencies. Governance draws the clear line between transformative innovation and unacceptable risk.
How does Deeploy handle different AI models and platforms?
Deeploy is designed for flexibility. It does not require you to migrate your existing AI models to a new platform. Instead, it connects to your current MLOps tools, cloud AI services, and GenAI platforms through integrations. This approach allows Deeploy to discover and onboard AI systems wherever they reside, providing a unified governance layer across your entire, diverse AI landscape without disrupting existing workflows.
Can Deeploy help with regulations beyond the EU AI Act?
Absolutely. While the EU AI Act is a key driver, Deeploy is built for a global regulatory environment. It includes default control frameworks based on international standards like ISO 42001 and the NIST AI Risk Management Framework. More importantly, it allows you to build custom control frameworks, meaning you can tailor the governance requirements to meet any regional, industrial, or internal corporate standard you need to follow.
Who within an organization should use Deeploy?
Deeploy serves multiple key roles. Compliance officers and risk managers use it to set policies and prove adherence. AI and engineering teams use it to understand and implement specific controls during development. Business leaders and product managers use the central registry and monitoring dashboards for oversight. Finally, auditors use the automated evidence trails for efficient reviews. It is a cross-functional platform for responsible AI scaling.
Threat Watch FAQ
How does Threat Watch evaluate cyber health?
Threat Watch evaluates cyber health by analyzing critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, providing a comprehensive assessment of an organization's cybersecurity posture.
Is Threat Watch suitable for all business sizes?
Yes, Threat Watch is designed to be beneficial for organizations of all sizes, from small businesses to large enterprises. Its scalable features allow it to adapt to various cybersecurity needs.
How often does Threat Watch update its assessments?
Threat Watch provides real-time insights and assessments, ensuring that organizations receive the most current information about their cybersecurity status and any emerging threats.
Can Threat Watch integrate with other cybersecurity tools?
Yes, Threat Watch is designed to integrate seamlessly with other cybersecurity tools and platforms, allowing organizations to create a cohesive cybersecurity strategy that enhances their overall protection.
Alternatives
Deeploy Alternatives
Deeploy is a specialized software platform in the AI governance and business intelligence category. It helps organizations manage the compliance, risk, and oversight of their artificial intelligence systems, ensuring they meet regulatory standards like the EU AI Act. Users may explore alternatives for several common reasons. These can include budget constraints, the need for different or more niche features, or a requirement for a platform that integrates with a specific existing technology stack. The search for the right tool is a normal part of the software evaluation process. When choosing an alternative, focus on core needs. Key considerations should be the platform's ability to provide visibility into all AI models, support for relevant compliance frameworks, and features for implementing real controls. The goal is to find a solution that turns governance from a concept into an enforceable, operational practice.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence solution designed to provide organizations with insights into their cyber health. It falls under the category of business intelligence, focusing specifically on enhancing cybersecurity through real-time assessments and comprehensive vulnerability scanning. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms and systems. When looking for an alternative, it is essential to consider factors such as the comprehensiveness of the security assessments, the capability for real-time monitoring, and the overall usability of the platform. Prioritizing features that align with your organization’s unique security needs can help ensure that the alternative chosen effectively safeguards sensitive information and mitigates potential risks.
