Karolium vs Threat Watch
Side-by-side comparison to help you choose the right product.
Karolium is a zero-code platform that empowers businesses to rapidly create and customize intelligent solutions for.
Last updated: February 28, 2026
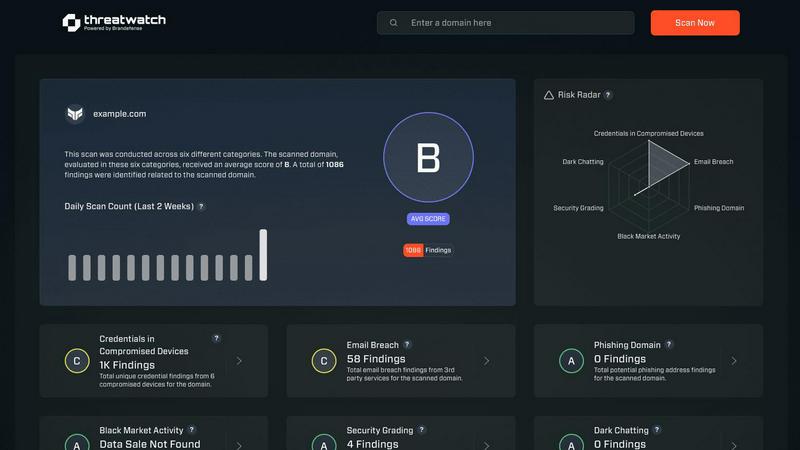
Threat Watch
Threat Watch quickly evaluates your cybersecurity health by identifying compromised accounts, devices, and dark web.
Last updated: March 1, 2026
Visual Comparison
Karolium

Threat Watch
Feature Comparison
Karolium
Zero-Code Development Environment
Karolium provides a user-friendly, zero-code environment that enables users to create applications without needing extensive technical knowledge. This feature democratizes app development, allowing business users to innovate and respond to needs quickly.
Built-in Predictive and Prescriptive Analytics
This platform comes equipped with advanced analytics tools that help organizations anticipate future trends and make informed decisions. The predictive and prescriptive capabilities guide users in optimizing workflows and enhancing operational efficiency.
Seamless Integration with Existing Systems
Karolium's robust integration capabilities allow businesses to connect their existing software ecosystems effortlessly. This feature ensures that organizations can extend the functionality of their current applications without extensive redevelopment.
Pre-composed Modules for Rapid Deployment
With ready-to-use, pre-composed modules, Karolium enables organizations to accelerate application development. These modules can be customized to fit specific workflows, reducing the time and resources required for deployment.
Threat Watch
Compromised Credentials Assessment
This feature allows organizations to automatically check for compromised credentials across various platforms. By monitoring leaked passwords and associated accounts, Threat Watch helps businesses identify accounts at risk, enabling them to take immediate action to secure their systems.
Vulnerable Device Identification
Threat Watch scans an organization's infrastructure to identify devices that are vulnerable to attacks. This includes evaluating the security status of all connected devices, ensuring that any potential weak points are addressed before they can be exploited by malicious actors.
Breached Account Monitoring
This feature continuously monitors known data breaches for any accounts associated with an organization. By providing alerts on compromised accounts, Threat Watch enables businesses to act swiftly to reset passwords and secure their digital assets, reducing the risk of unauthorized access.
Phishing Address Detection
Threat Watch actively identifies and flags known phishing addresses that may target the organization. By providing insights into potential phishing threats, businesses can educate their employees on recognizing these attempts, thus enhancing overall cybersecurity awareness.
Use Cases
Karolium
Enhancing Operational Efficiency
Businesses can utilize Karolium to create tailored applications that streamline operations and automate repetitive tasks. This leads to significant time savings and improved productivity across various departments.
Accelerating Digital Transformation
Organizations looking to undergo digital transformation can leverage Karolium to build and deploy new applications rapidly. This allows them to keep pace with market changes and adopt innovative technologies without the challenges of traditional coding.
Improving Data-Driven Decision Making
Karolium's analytics tools enable companies to harness data effectively, allowing them to make informed decisions based on real-time insights. This capability is crucial for organizations striving to remain competitive in their industries.
Facilitating Collaboration Across Teams
Karolium empowers businesses to create applications that enhance collaboration among teams. By providing a shared platform for communication and project management, organizations can break down silos and foster a more cohesive work environment.
Threat Watch
Small Business Cybersecurity
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides them with essential tools to monitor their cyber health, ensuring that they can identify vulnerabilities without overwhelming their limited resources.
Enterprise Risk Management
Large enterprises can utilize Threat Watch to maintain a comprehensive overview of their cybersecurity landscape. The tool’s real-time monitoring and assessment capabilities help in prioritizing risks across multiple departments and locations.
Incident Response Planning
Organizations can leverage Threat Watch to improve their incident response strategies. By understanding the vulnerabilities within their systems, businesses can develop tailored response plans, ensuring they are prepared to address potential cyber incidents effectively.
Cybersecurity Training and Awareness
Threat Watch helps organizations enhance employee awareness of cybersecurity threats. By identifying phishing addresses and compromised credentials, businesses can create training sessions that educate staff on recognizing and reporting potential threats.
Overview
About Karolium
Karolium is a next-generation zero-code platform that revolutionizes the way businesses develop customized applications. By eliminating the need for traditional coding skills, Karolium empowers organizations to build, extend, and customize intelligent business solutions rapidly. This unified platform integrates capabilities of iPaaS, aPaaS, oPaaS, and AIPaaS, allowing users to leverage ready-to-deploy modules for creating applications that meet specific operational needs. Ideal for businesses seeking to enhance agility and efficiency, Karolium offers built-in predictive and prescriptive analytics that guide firms through their unique challenges. Its seamless integration capabilities ensure that businesses can adapt their applications to changing market demands while maintaining competitiveness in a dynamic digital landscape.
About Threat Watch
Threat Watch is a comprehensive cybersecurity intelligence solution aimed at empowering organizations to actively monitor and enhance their cyber health. By evaluating critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, Threat Watch provides users with a holistic view of their cybersecurity landscape. This tool is designed for businesses of all sizes, from small startups to large enterprises, helping them identify and prioritize potential risks effectively. The main value proposition of Threat Watch lies in its ability to deliver real-time insights and automated assessments, enabling organizations to quickly uncover vulnerabilities and exposures. By doing so, businesses can take proactive measures to mitigate risks and safeguard sensitive information, ensuring that they remain resilient against cyber threats. With Threat Watch, users gain clarity in their cybersecurity posture, allowing for swifter and more efficient responses to emerging threats.
Frequently Asked Questions
Karolium FAQ
What industries can benefit from using Karolium?
Karolium is designed for a wide range of industries, including manufacturing, retail, healthcare, and finance. Its versatility and zero-code capabilities make it suitable for any organization looking to enhance operational efficiency.
How does Karolium ensure data security?
Karolium prioritizes data security by implementing robust encryption and compliance measures. The platform adheres to industry standards, ensuring that sensitive information is protected throughout the application lifecycle.
Can I integrate Karolium with my existing software?
Yes, Karolium offers seamless integration capabilities that allow businesses to connect with their existing software solutions. This ensures that users can enhance their current systems without the need for extensive redevelopment.
Is training required to use Karolium?
Karolium's zero-code environment is designed to be user-friendly, minimizing the need for extensive training. However, users are encouraged to participate in introductory sessions to maximize their understanding of the platform's capabilities.
Threat Watch FAQ
How does Threat Watch evaluate cyber health?
Threat Watch evaluates cyber health by analyzing critical security categories such as compromised credentials, vulnerable devices, breached accounts, and phishing addresses, providing a comprehensive assessment of an organization's cybersecurity posture.
Is Threat Watch suitable for all business sizes?
Yes, Threat Watch is designed to be beneficial for organizations of all sizes, from small businesses to large enterprises. Its scalable features allow it to adapt to various cybersecurity needs.
How often does Threat Watch update its assessments?
Threat Watch provides real-time insights and assessments, ensuring that organizations receive the most current information about their cybersecurity status and any emerging threats.
Can Threat Watch integrate with other cybersecurity tools?
Yes, Threat Watch is designed to integrate seamlessly with other cybersecurity tools and platforms, allowing organizations to create a cohesive cybersecurity strategy that enhances their overall protection.
Alternatives
Karolium Alternatives
Karolium is a zero-code platform that plays a vital role in the development of customizable applications, enabling businesses to achieve digital transformation without requiring traditional programming skills. This platform is designed to streamline the creation of tailored applications, making it an attractive option for organizations seeking to enhance their operational efficiency and adaptability in a competitive environment. Users often seek alternatives to Karolium due to various reasons, including pricing concerns, specific feature requirements, or unique platform needs that may not be fully met. When considering an alternative, it's essential to evaluate factors such as ease of use, integration capabilities, the flexibility of customization options, and the overall support offered by the provider. These elements can significantly impact the success of a digital transformation initiative.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence solution designed to provide organizations with insights into their cyber health. It falls under the category of business intelligence, focusing specifically on enhancing cybersecurity through real-time assessments and comprehensive vulnerability scanning. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms and systems. When looking for an alternative, it is essential to consider factors such as the comprehensiveness of the security assessments, the capability for real-time monitoring, and the overall usability of the platform. Prioritizing features that align with your organization’s unique security needs can help ensure that the alternative chosen effectively safeguards sensitive information and mitigates potential risks.